Overview
Network Time Protocol (NTP) is the backbone of time synchronization across your infrastructure. Accurate, consistent time is essential for log correlation, certificate validation, routing protocol behaviour, and security auditing. This run book covers every aspect of NTP configuration on Cisco IOS and IOS-XE platforms — from basic client setup through authenticated hierarchical deployments.
NTP Stratum Hierarchy
NTP operates in a layered hierarchy called stratum levels:
- Stratum 0 — Atomic clocks and GPS receivers (hardware reference)
- Stratum 1 — Servers directly synced to stratum 0 (public NTP pools)
- Stratum 2 — Internal servers synced to stratum 1
- Stratum 3+ — Downstream clients syncing from stratum 2
Stratum 16 means unsynchronized. Cisco routers can act as both NTP clients (syncing upstream) and NTP servers (serving downstream devices).
Lab Topology
Public NTP (203.0.113.1) [Stratum 1]
|
sw-infrarunbook-core-01 [Stratum 2 — NTP Server]
192.168.10.1 / Lo0: 10.255.255.1
|
+-------+-------+
| |
sw-infrarunbook-dist-01 sw-infrarunbook-dist-02
192.168.10.2 192.168.10.3
[Stratum 3 Clients]Step 1 — Configure NTP Client (Basic)
Sync a Cisco device to an external NTP server:
sw-infrarunbook-core-01# configure terminal
sw-infrarunbook-core-01(config)# ntp server 203.0.113.1 prefer
sw-infrarunbook-core-01(config)# ntp server 203.0.113.2
sw-infrarunbook-core-01(config)# end- prefer — marks this as the primary source when multiple servers are configured
- Configuring two or more servers provides redundancy; NTP selects the best source via the Marzullo clock-selection algorithm
Step 2 — Configure NTP Master (Local Authoritative Source)
When no external NTP source is available, configure the device as a local clock master:
sw-infrarunbook-core-01(config)# ntp master 3- Stratum value 3 is typical for an internal fallback master
- Never use
ntp master 1
— stratum 1 implies a hardware reference clock - Use
ntp master
only as a fallback; always prefer a real upstream NTP source
Best practice: Configure at least two external NTP servers plusntp master 3as local fallback. This ensures devices never go unsynchronized even during upstream outages.
Step 3 — Configure Downstream NTP Clients
Distribution and access layer devices should sync from the core rather than directly from the internet:
sw-infrarunbook-dist-01(config)# ntp server 192.168.10.1 prefer
sw-infrarunbook-dist-01(config)# ntp server 192.168.10.2
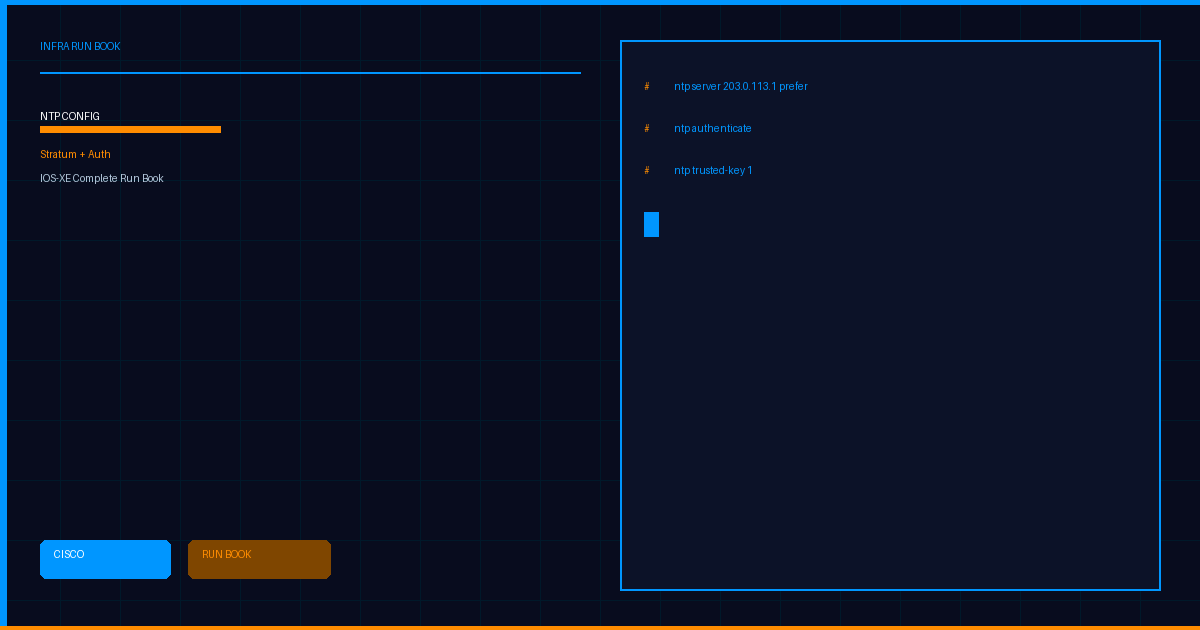
sw-infrarunbook-dist-01(config)# ntp master 5Step 4 — Configure NTP Authentication (MD5)
NTP authentication prevents rogue devices from injecting false time. Always enable in production environments.
On the NTP Server (sw-infrarunbook-core-01):
sw-infrarunbook-core-01(config)# ntp authenticate
sw-infrarunbook-core-01(config)# ntp authentication-key 1 md5 Infr@NTP2024!
sw-infrarunbook-core-01(config)# ntp trusted-key 1On the NTP Client (sw-infrarunbook-dist-01):
sw-infrarunbook-dist-01(config)# ntp authenticate
sw-infrarunbook-dist-01(config)# ntp authentication-key 1 md5 Infr@NTP2024!
sw-infrarunbook-dist-01(config)# ntp trusted-key 1
sw-infrarunbook-dist-01(config)# ntp server 192.168.10.1 key 1 preferntp authenticate
— enforces authentication; rejects unauthenticated packetsntp authentication-key <id> md5 <password>
— defines the MD5 keyntp trusted-key <id>
— marks key as trusted for synchronizationntp server <ip> key <id>
— associates the key with a specific upstream server
Security note: NTP keys are stored in running-config as plain text by default. Useservice password-encryptionto obfuscate them, and disableip http serverto prevent config exposure via HTTP.
Step 5 — Set Timezone and Clock
sw-infrarunbook-core-01(config)# clock timezone UTC 0Best practice: Always configure all devices in UTC. Application layers handle local timezone conversion. Mixed timezones cause log correlation failures during incident response.
Manually Set the Hardware Clock (if clock is badly drifted):
sw-infrarunbook-core-01# clock set 10:30:00 12 Mar 2026
sw-infrarunbook-core-01# clock update-calendarStep 6 — NTP Access Control (Access Groups)
Restrict which devices can query or synchronize from your NTP server:
sw-infrarunbook-core-01(config)# access-list 50 permit 192.168.0.0 0.0.255.255
sw-infrarunbook-core-01(config)# access-list 50 permit 10.0.0.0 0.255.255.255
sw-infrarunbook-core-01(config)# ntp access-group serve-only 50Access Group Levels (most to least permissive):
- peer — full bidirectional synchronization and querying
- serve — allows time sync requests and queries
- serve-only — allows only time synchronization (no query)
- query-only — allows NTP queries but not synchronization
! Peer relationship with another core router
access-list 20 permit host 192.168.10.2
! Serve-only for distribution layer
access-list 21 permit 192.168.10.0 0.0.0.255
sw-infrarunbook-core-01(config)# ntp access-group peer 20
sw-infrarunbook-core-01(config)# ntp access-group serve-only 21Step 7 — Configure NTP Source Interface
NTP packets should originate from a stable loopback interface to maintain sessions during physical link failures:
sw-infrarunbook-core-01(config)# interface Loopback0
sw-infrarunbook-core-01(config-if)# ip address 10.255.255.1 255.255.255.255
sw-infrarunbook-core-01(config-if)# exit
sw-infrarunbook-core-01(config)# ntp source Loopback0Step 8 — NTP Broadcast Mode (Optional)
For large flat networks, broadcast mode reduces unicast NTP configuration overhead:
Server side:
sw-infrarunbook-core-01(config)# interface GigabitEthernet0/1
sw-infrarunbook-core-01(config-if)# ntp broadcastClient side:
sw-infrarunbook-dist-01(config)# interface GigabitEthernet0/1
sw-infrarunbook-dist-01(config-if)# ntp broadcast clientWarning: NTP broadcast is less secure than unicast. Only use on trusted internal segments and always combine with NTP authentication.
Verification Commands
Check NTP Status:
sw-infrarunbook-core-01# show ntp status
Clock is synchronized, stratum 2, reference is 203.0.113.1
nominal freq is 250.0000 Hz, actual freq is 250.0002 Hz, precision is 2**10
ntp uptime is 43200 (1/100 of seconds), resolution is 4000
reference time is E7A5C3B1.12345678 (10:15:33.071 UTC Thu Mar 12 2026)
clock offset is 0.5000 msec, root delay is 4.50 msec
root dispersion is 7.63 msec, peer dispersion is 0.80 msec
loopfilter state is 'CTRL' (Normal Controlled Loop), drift is 0.000000001 s/s
system poll interval is 1024, last update was 512 sec ago.- Clock is synchronized — NTP is working correctly
- stratum 2 — this device's current stratum level
- reference is 203.0.113.1 — the active upstream peer
- clock offset — time difference from reference (should be < 128 ms in production)
Check NTP Associations:
sw-infrarunbook-core-01# show ntp associations
address ref clock st when poll reach delay offset disp
*~203.0.113.1 .GPS. 1 64 1024 377 4.50 0.500 0.800
~203.0.113.2 .GPS. 1 128 1024 377 5.20 0.700 0.900
* sys.peer, # selected, + candidate, - outlyer, x falseticker, ~ configured- * — currently selected system peer
- ~ — manually configured server
- reach 377 — octal: all 8 recent polls succeeded (maximum)
- reach 0 — no recent polls succeeded (connectivity or auth issue)
Check NTP Associations Detail:
sw-infrarunbook-core-01# show ntp associations detail
203.0.113.1 configured, authenticated, our_master, sane, valid, stratum 1
ref ID .GPS., time E7A5C3B1.12345678 (10:15:33.071 UTC Thu Mar 12 2026)
our mode client, peer mode server, our poll intvl 1024, peer poll intvl 1024
root delay 2.00 msec, root disp 3.00, reach 377, sync dist 7.63
delay 4.50 msec, offset 0.500 msec, dispersion 0.80
filtdelay = 4.50 4.60 4.55 4.48 4.52 4.51 4.49 4.53
filtoffset = 0.50 0.48 0.51 0.49 0.50 0.51 0.49 0.50Look for the word authenticated in the output to confirm MD5 authentication is working.
Troubleshooting Common NTP Issues
Issue 1: "Clock is unsynchronized"
! Verify reachability to NTP server
sw-infrarunbook-core-01# ping 203.0.113.1 source Loopback0
! Check if UDP 123 is permitted in ACLs
sw-infrarunbook-core-01# show ip access-lists
! Check reach field — if 0, no packets are getting through
sw-infrarunbook-core-01# show ntp associationsIssue 2: Authentication failure — "peer is not authenticated"
! Verify key ID and password match on both devices
sw-infrarunbook-core-01# show running-config | include ntp
! Ensure ntp authenticate is enabled and key is trusted
sw-infrarunbook-core-01(config)# ntp authenticate
sw-infrarunbook-core-01(config)# ntp trusted-key 1
! Look for 'authenticated' in association detail
sw-infrarunbook-core-01# show ntp associations detailIssue 3: Stratum 16 (unsynchronized)
! Stratum 16 = not synchronized to any valid source
! Add local fallback master
sw-infrarunbook-core-01(config)# ntp master 3
! Check if upstream servers are reachable and responding
sw-infrarunbook-core-01# show ntp associations detailIssue 4: Large clock offset (> 1000 seconds — panic threshold)
! NTP will not adjust offsets > 1000 seconds (panic threshold)
! Manually correct the clock first, then NTP takes over
sw-infrarunbook-core-01# clock set 10:30:00 12 Mar 2026
sw-infrarunbook-core-01# show ntp statusDebug NTP (use sparingly in production):
sw-infrarunbook-core-01# debug ntp all
! ... observe output ...
sw-infrarunbook-core-01# undebug allComplete Production NTP Configuration
Core Router / NTP Server (sw-infrarunbook-core-01):
! ============================================================
! NTP — sw-infrarunbook-core-01
! Role: Internal NTP Server + Upstream NTP Client
! ============================================================
clock timezone UTC 0
interface Loopback0
ip address 10.255.255.1 255.255.255.255
! Authentication
ntp authenticate
ntp authentication-key 1 md5 Infr@NTP2024!
ntp trusted-key 1
! Upstream NTP (stratum 1 public servers)
ntp server 203.0.113.1 key 1 prefer
ntp server 203.0.113.2 key 1
! Local master fallback (stratum 3)
ntp master 3
! Use loopback as source
ntp source Loopback0
! Restrict NTP service to internal subnets only
access-list 50 permit 192.168.0.0 0.0.255.255
access-list 50 permit 10.0.0.0 0.255.255.255
ntp access-group serve-only 50Distribution Switch / NTP Client (sw-infrarunbook-dist-01):
! ============================================================
! NTP — sw-infrarunbook-dist-01
! Role: NTP Client (syncs from core)
! ============================================================
clock timezone UTC 0
ntp authenticate
ntp authentication-key 1 md5 Infr@NTP2024!
ntp trusted-key 1
ntp server 10.255.255.1 key 1 prefer
ntp server 192.168.10.1 key 1
! Local fallback at low priority
ntp master 5IOS-XE Specific Notes (Catalyst 9000 / ASR 1000)
- All NTP CLI commands above apply identically to IOS-XE
- Catalyst 9300/9500 support IEEE 1588 PTP in addition to NTP — check with
show ptp clock
- For hardware-assisted timestamping on ASR 1000, verify with
show platform ntp
- IOS-XE 17.x+ — no syntax changes;
show ntp status
andshow ntp associations
remain unchanged - On Catalyst 9000 stacks, NTP syncs through the active member; standby members follow
Quick Reference: Key NTP Commands
! Status
show ntp status
show ntp associations
show ntp associations detail
show clock detail
! Configuration
show running-config | section ntp
show running-config | include ntp
! Debug
debug ntp all
debug ntp packets
undebug allFrequently Asked Questions
What is the difference between ntp server and ntp master on Cisco IOS?
ntp serverconfigures the device to synchronize its clock from an external NTP source.
ntp mastermakes the device act as an authoritative time source using its internal clock — it serves time to downstream devices even without an upstream reference. Use
ntp masteronly as a fallback, since the local clock drifts more than a real stratum 1/2 server.
What stratum value should I set for ntp master?
Use stratum 3 or higher (e.g.,
ntp master 3) for a core router that also syncs from external stratum 1 sources. Never configure
ntp master 1— that value implies a hardware reference clock (GPS or atomic). For pure fallback-only masters with no upstream, stratum 5 is a reasonable choice to avoid polluting the hierarchy.
Why does my NTP association show "reach 0"?
Reach 0 means no NTP packets have been received from that server. Common causes: UDP port 123 blocked by an ACL or firewall, the NTP server IP is unreachable (check routing), the server IP is incorrect, or NTP authentication mismatch is causing all received packets to be dropped silently. Use
debug ntp packetsto confirm packet flow.
Can I use NTP authentication with public NTP pool servers?
Most public NTP servers (pool.ntp.org, time.cloudflare.com, etc.) do not support MD5 authentication — they serve unauthenticated NTP to all clients. NTP MD5 authentication is practical only for servers you control. For public upstream servers, rely on NTP access groups and perimeter firewall rules instead of per-server authentication.
What is the NTP panic threshold?
By default, NTP refuses to adjust the clock if the offset exceeds 1000 seconds. This prevents accidental large time jumps that could break certificate validation or database transactions. If a device clock is more than 1000 seconds off, manually correct it with
clock setfirst, then NTP will take over once the offset is within the threshold.
How do I confirm NTP authentication is working?
Run
show ntp associations detailand check for the word
authenticatedin the server's status line. If authentication fails, the association will show
insaneand the device will never reach synchronized state. Also check that both
ntp authenticateand
ntp trusted-keyare configured with identical key IDs and passwords on both ends.
What does the "reach" field mean in show ntp associations?
Reach is an 8-bit shift register displayed in octal. Each successful poll shifts a binary 1 into the register; each failed poll shifts a 0. A value of 377 (octal) means all 8 most recent polls succeeded. A value of 376 means the last poll failed. A value of 0 means no recent polls succeeded and the server is effectively unreachable.
Should I point all devices directly at external NTP servers?
No — configure a hierarchical model. Core routers sync from 2–3 external NTP servers and act as internal NTP servers. Distribution and access switches sync from the core. This reduces external NTP traffic, centralizes authentication key management, and ensures downstream devices maintain synchronization even if external connectivity is lost (via
ntp masterfallback).
What is the ntp source command and why should I use a loopback?
ntp source <interface>specifies which interface IP is used as the source address in outbound NTP packets. Using a loopback interface is strongly recommended: loopback IPs are always up as long as the device is running, preventing NTP session resets during physical link failures. Without this, a link failure on the sourcing interface causes NTP to reset and re-establish sessions.
How do I prevent external hosts from using my router as an NTP server?
Create an ACL that permits only your internal subnets, then apply it with
ntp access-group serve-only <acl>. This allows internal devices to sync time from the router while blocking all external NTP queries. For internet-facing routers, also ensure UDP port 123 inbound is blocked at the perimeter firewall for all but the intended upstream NTP server IPs.
What happens if I forget to configure ntp master and all upstream servers fail?
Without
ntp master, if all configured upstream servers become unreachable, the device clock free-runs on its internal oscillator. The clock drifts gradually — typically 10–100 ms per day depending on platform. Downstream devices that sync from this device will also lose synchronization and eventually show stratum 16. Always configure
ntp master 5as a last-resort fallback.
Does NTP work over IPv6 on Cisco IOS-XE?
Yes. Use
ntp server ipv6 2001:DB8::1to configure an IPv6 NTP server. Authentication and access groups function identically to IPv4. Ensure IPv6 unicast routing is enabled, the NTP server IPv6 address is reachable, and UDP port 123 is permitted for IPv6 traffic in your ACL policy.
Related Articles
- [Cisco] Cisco SNMP Configuration: Complete Run Book for SNMPv2c, SNMPv3, Traps, and Polling on IOS/IOS-XE
- [Cisco] Cisco AAA with TACACS+ and RADIUS: Complete Run Book for Authentication, Authorization, and Accounting on IOS/IOS-XE
- [Cisco] Cisco Zone-Based Firewall (ZBF): Complete Run Book for IOS/IOS-XE Policy Configuration
- [Cisco] Cisco NAT/PAT Configuration: Complete Run Book for Static NAT, Dynamic NAT, PAT Overload, and Policy NAT on IOS/IOS-XE