What Spanning Tree Actually Is
Spanning Tree Protocol — STP — exists for one reason: to prevent Layer 2 loops. If you've ever accidentally created a loop on a switch network without STP running, you've watched a broadcast storm consume every available CPU cycle and bring the network to its knees in seconds. STP solves this by logically blocking redundant paths while keeping them physically connected, ready to take over the moment the active path fails.
The original STP standard is IEEE 802.1D, and it's been around since the late 1980s. It works, but it's slow — sometimes painfully slow. RSTP (Rapid Spanning Tree Protocol, 802.1w) replaced it with dramatically faster convergence. MSTP (Multiple Spanning Tree Protocol, 802.1s) went further still by allowing multiple logical topologies to coexist over the same physical infrastructure. Cisco layered its own extensions on top with PVST+ (Per-VLAN Spanning Tree Plus) and Rapid PVST+, running these standards independently per VLAN.
Understanding all three isn't just academic. In my experience, most STP-related outages come from engineers who understood just enough to configure it but not enough to troubleshoot it when something goes sideways at 2am.
How Classic STP (802.1D) Works
STP builds a loop-free topology by electing a root bridge and determining the shortest path from every other switch back to that root. The protocol uses Bridge Protocol Data Units — BPDUs — which are control frames exchanged between switches to share topology information. The root bridge generates BPDUs every 2 seconds, and they propagate downstream through the network.
Every switch participates in a root bridge election. The switch with the lowest Bridge ID wins. The Bridge ID is an 8-byte value: a 2-byte bridge priority combined with the switch's MAC address. The default priority is 32768, which means if you haven't explicitly tuned anything, whichever switch has the lowest MAC address becomes your root. That's often not your best switch — it's frequently the oldest one, since earlier hardware tends to carry lower OUI-assigned MAC addresses.
Once the root is elected, each non-root switch selects a root port — the port offering the best-cost path back to the root. Each network segment elects a designated port, which is the port on that segment closest to the root. Every remaining port that's neither a root port nor a designated port gets blocked. Blocked ports don't forward user traffic but still listen for BPDUs, sitting ready to transition if the topology changes.
STP port states in 802.1D flow through: Blocking → Listening → Learning → Forwarding (and Disabled for administratively shut ports). The transition from Blocking all the way to Forwarding takes 30 seconds by default — 15 seconds in Listening and 15 seconds in Learning, governed by the Forward Delay timer. Add in the Max Age timer at 20 seconds for detecting a dead root, and you're looking at up to 50 seconds for full convergence after a topology change. For modern networks, that's an eternity.
Cisco's PVST+ runs a separate STP instance per VLAN. This matters because you can engineer the topology so that different VLANs prefer different uplinks — effectively load-balancing across redundant links at Layer 2. The tradeoff is CPU and memory overhead, since each VLAN maintains its own independent process.
RSTP: The Same Idea, Done Properly Fast
RSTP (802.1w) is where things get genuinely better. It's not just adjusted timers — it's a fundamentally different convergence mechanism. Instead of waiting passively through timer-based state transitions, RSTP uses a negotiation handshake called the proposal/agreement mechanism. When a designated port wants to enter Forwarding, it sends a Proposal BPDU to its downstream neighbor. The neighbor agrees — meaning it will block its own downstream ports first to ensure no loop forms — and responds with an Agreement BPDU. The port transitions to Forwarding immediately. This sync propagates outward from the root and typically converges in well under a second.
RSTP also defines cleaner port roles. You have the Root Port (best path to root), Designated Port (best port on a segment toward downstream bridges), Alternate Port (a backup root port that can take over instantly if the root port fails), and Backup Port (a redundant designated port on the same segment). Port states are simplified to three: Discarding, Learning, and Forwarding. The old Listening state is eliminated — it was functionally redundant.
Edge ports are a key RSTP concept. If you configure a port as an edge port — what Cisco calls PortFast — RSTP treats it as a port that will never connect to another bridge. It skips proposal/agreement entirely and goes straight to Forwarding. Crucially, if an edge port receives a BPDU, it immediately loses its edge port status and rejoins normal STP operation. That's an important self-healing behavior that classic STP lacks.
Cisco implements RSTP as Rapid PVST+. Like PVST+, it runs one instance per VLAN. For most deployments — campus networks, enterprise branches, data center access layers — Rapid PVST+ is the right default choice.
MSTP: Multiple Instances, Smarter at Scale
MSTP (802.1s) addresses a specific scaling problem. If you're running Rapid PVST+ with 200 VLANs, you have 200 independent spanning tree instances running on every switch in your network. That's 200 sets of BPDUs being generated and processed, 200 topology databases maintained in memory, and meaningful CPU overhead — especially on older or lower-end switching hardware.
MSTP solves this by letting you map multiple VLANs to a single spanning tree instance. Instead of one instance per VLAN, you define MST Instances (MSTIs), each managing a group of VLANs sharing one logical topology. VLANs not explicitly mapped fall into Instance 0, called the Internal Spanning Tree (IST). The IST also handles interoperability with non-MSTP switches at region boundaries.
MSTP groups switches into MST regions. Two switches are in the same region only if they share an identical region name, revision number, and VLAN-to-instance mapping table. Switches in different regions appear to each other as a single virtual bridge running a simplified 802.1D-compatible topology. This abstraction is elegant for scale, but it's also a common source of misconfiguration headaches. I'll cover that in the misconceptions section.
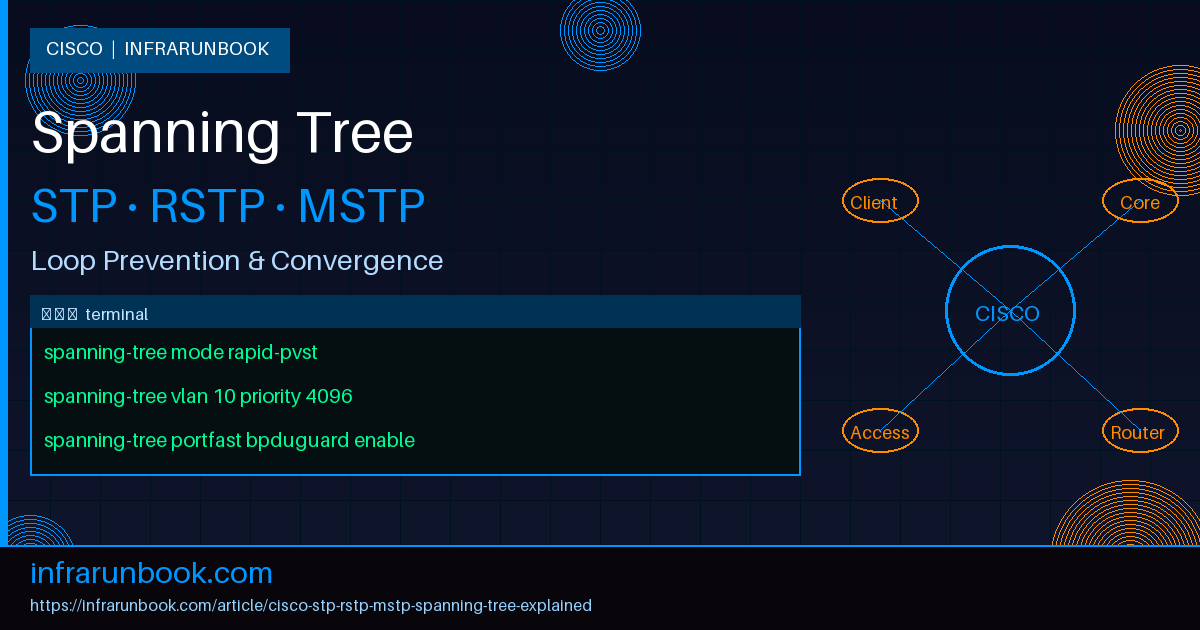
Configuring STP and RSTP on sw-infrarunbook-01
The first rule of production STP: always set your root bridge explicitly. Never leave it to MAC address lottery. On sw-infrarunbook-01, which is your intended root for VLANs 10, 20, and 30, start by switching to Rapid PVST+ and setting a lower priority:
sw-infrarunbook-01# configure terminal
sw-infrarunbook-01(config)# spanning-tree mode rapid-pvst
sw-infrarunbook-01(config)# spanning-tree vlan 10,20,30 priority 4096Alternatively, the
root primarymacro does this automatically — it sets priority to 24576 or lower if another switch is already claiming that value. If you want predictability, set the priority directly. Bridge priorities must be multiples of 4096, so valid values are 0, 4096, 8192, 12288, and so on up to 61440.
sw-infrarunbook-01(config)# spanning-tree vlan 10,20,30 root primary
sw-infrarunbook-01(config)# spanning-tree vlan 40,50 root secondaryFor access ports facing end devices — workstations, phones, printers — you always want PortFast and BPDU Guard enabled together. PortFast skips Listening and Learning for immediate Forwarding. BPDU Guard err-disables the port if it ever receives a BPDU, protecting against someone plugging an unmanaged switch into an access port and accidentally introducing a loop or a rogue root bridge candidate.
sw-infrarunbook-01(config)# interface GigabitEthernet0/1
sw-infrarunbook-01(config-if)# switchport mode access
sw-infrarunbook-01(config-if)# switchport access vlan 10
sw-infrarunbook-01(config-if)# spanning-tree portfast
sw-infrarunbook-01(config-if)# spanning-tree bpduguard enableYou can also enable PortFast and BPDU Guard globally for all access ports, which is cleaner at scale:
sw-infrarunbook-01(config)# spanning-tree portfast default
sw-infrarunbook-01(config)# spanning-tree portfast bpduguard defaultOn trunk uplinks to other switches, you want Root Guard on ports that should never become root ports. Root Guard causes a port to enter Root-Inconsistent state if it receives a superior BPDU — effectively preventing a downstream switch from winning the root election — and it recovers automatically once the superior BPDUs stop arriving.
sw-infrarunbook-01(config)# interface GigabitEthernet0/24
sw-infrarunbook-01(config-if)# switchport mode trunk
sw-infrarunbook-01(config-if)# spanning-tree guard rootFor root ports and alternate ports on distribution-facing uplinks, Loop Guard is worth enabling. It protects against unidirectional link failures — scenarios where a fiber strand breaks in one direction, causing a port to stop receiving BPDUs even though it can still transmit. Without Loop Guard, that port would eventually transition to Designated/Forwarding, potentially creating a loop. With Loop Guard, it enters Loop-Inconsistent state instead and blocks. Enable it globally or per-interface:
sw-infrarunbook-01(config)# spanning-tree loopguard defaultConfiguring MSTP on sw-infrarunbook-01
Switching to MSTP mode requires careful coordination across all switches in the region. The name, revision number, and VLAN-to-instance mapping must be identical on every switch you want in the same region. A single character mismatch in the region name puts those switches in different regions, and the topology changes in ways that aren't always obvious from a quick glance at interface states.
Here's a sample MSTP configuration that splits 40 VLANs across two instances to allow load balancing across dual uplinks:
sw-infrarunbook-01(config)# spanning-tree mode mst
sw-infrarunbook-01(config)# spanning-tree mst configuration
sw-infrarunbook-01(config-mst)# name solvethenetwork
sw-infrarunbook-01(config-mst)# revision 1
sw-infrarunbook-01(config-mst)# instance 1 vlan 10-20
sw-infrarunbook-01(config-mst)# instance 2 vlan 21-40
sw-infrarunbook-01(config-mst)# exit
sw-infrarunbook-01(config)# spanning-tree mst 1 priority 4096
sw-infrarunbook-01(config)# spanning-tree mst 2 priority 8192On your secondary switch, invert the priorities so it becomes root for Instance 2 while sw-infrarunbook-01 remains root for Instance 1. That's how you get genuine load balancing across your uplinks — different VLANs take different physical paths.
To verify your spanning tree state, these are the commands I reach for first in any troubleshooting session:
sw-infrarunbook-01# show spanning-tree vlan 10
sw-infrarunbook-01# show spanning-tree detail
sw-infrarunbook-01# show spanning-tree inconsistentports
sw-infrarunbook-01# show spanning-tree mst
sw-infrarunbook-01# show spanning-tree mst 1 detail
sw-infrarunbook-01# show spanning-tree summaryThe
show spanning-tree detailoutput tells you the root bridge MAC, active timers, port roles, and state for every VLAN. The
inconsistentportscommand is your first stop during any loop investigation — it shows ports stuck in Root-Inconsistent or Loop-Inconsistent state that might be silently blocking traffic.
Timer Tuning and Network Diameter
In classic STP, the Hello, Forward Delay, and Max Age timers are set on the root bridge and propagated downstream via BPDUs. The defaults — Hello 2s, Forward Delay 15s, Max Age 20s — are calculated for a maximum network diameter of seven switches. If your topology is deeper than seven hops, you need to adjust these values on the root bridge. That said, in any network running Rapid PVST+ or MSTP, timer tuning is rarely necessary because the proposal/agreement mechanism doesn't rely on timers for convergence.
If you do tune timers, the relationships between them must hold: Max Age must be greater than or equal to 2 × (Hello Time + 1), and Forward Delay must be greater than or equal to (Max Age / 2) + 1. Cisco's IOS won't always stop you from configuring values that violate these relationships, so you need to verify manually. Here's a safe set of tuned timers for a three-tier hierarchy that wants slightly faster failure detection:
sw-infrarunbook-01(config)# spanning-tree vlan 10,20,30 hello-time 1
sw-infrarunbook-01(config)# spanning-tree vlan 10,20,30 forward-time 10
sw-infrarunbook-01(config)# spanning-tree vlan 10,20,30 max-age 14Lowering the hello timer to 1 second cuts the root-failure detection window from 6 seconds down to 3 (three missed hellos), at the cost of doubling BPDU processing load across all switches. It's a reasonable trade-off in a well-tuned campus core, but you don't need it if RSTP's sub-second convergence is already meeting your availability requirements.
Why This Matters in Production
STP isn't glamorous, but get it wrong and it looks like a DDoS. Broadcast storms are vicious — a single Layer 2 loop can saturate every link in a broadcast domain in under a second. I've seen a single unmanaged consumer switch, bridging two access ports on the same VLAN, take down a 400-user office network in the time it takes to walk from the server room to the wiring closet. No STP, no protection, instant meltdown.
Convergence speed during failures is the other side of this. If your root bridge loses power unexpectedly, every switch needs to re-elect a new root and recalculate the forwarding topology. With classic STP, that's 30–50 seconds of complete blackout while timers expire. With Rapid PVST+, it's typically under 2 seconds. For anything running VoIP, real-time video, or database replication over Layer 2, that delta is the difference between a tolerable blip and a flood of incident tickets.
MSTP becomes relevant at scale — service provider edge networks, data centers running hundreds of VLANs, or environments where switch CPU is a meaningful constraint. For a typical enterprise campus with 20 VLANs on 30 switches, Rapid PVST+ is the right tool. For a provider network carrying 500 VLANs across 200 switches, reducing those 500 independent BPDU streams to a handful of MST instances is worth the configuration complexity.
Common Misconceptions
"STP is disabled by default on Cisco switches." It isn't. STP is on by default for all VLANs. You'd have to explicitly disable it per VLAN with
no spanning-tree vlan <id>, which you should never do unless you have a deliberate loop prevention alternative in place — like vPC peer-links or a routed access layer.
"PortFast disables STP on the port." It doesn't. PortFast skips the Listening and Learning states to reach Forwarding faster, but the port still participates in STP. If the port receives a BPDU, RSTP factors it into its topology calculation. BPDU Guard is what actually shuts the port down when unexpected BPDUs arrive — and pairing both together on access ports is the correct pattern.
"The root bridge should be your fastest switch." Not exactly. It should be your most central and most stable switch — typically the core or distribution layer. The root bridge is the reference point toward which all other switches calculate their paths, so placing it at the topological center minimizes traffic detours. Putting it at an edge because it happens to have the most ports or fastest backplane produces suboptimal traffic flows across the entire Layer 2 domain.
"MSTP is always better than Rapid PVST+." It depends entirely on scale. MSTP adds genuine complexity — region naming, revision numbers, instance mappings that must stay synchronized across every switch in the region. A one-character mismatch in the region name is enough to create separate MST regions, change the topology, and drop traffic in ways that are genuinely difficult to diagnose. If your VLAN count doesn't justify it, Rapid PVST+'s simplicity wins every time.
"Loop Guard and BPDU Guard do the same thing." They protect against completely different failure modes. BPDU Guard err-disables a port when it receives a BPDU unexpectedly — it's designed for PortFast access ports facing end devices. Loop Guard protects against unidirectional link failures on switch-to-switch links — if a port that should be receiving BPDUs stops getting them, Loop Guard puts it in Loop-Inconsistent state instead of letting it transition to Forwarding. They can and should coexist on different port types in the same network.
"Rapid PVST+ and classic PVST+ interoperate seamlessly." They do interoperate, but not without a cost. When a Rapid PVST+ switch connects to a classic STP switch on a trunk, the RSTP switch falls back to 802.1D behavior on that link. You lose all the fast convergence benefits of RSTP for that segment. The fallback is by design — IEEE mandated backward compatibility — but it catches engineers off guard when they're troubleshooting slow failover on a link they assumed was running RSTP end-to-end.
Spanning tree is one of those protocols that works quietly in the background until it catastrophically doesn't. The engineers who never have STP emergencies aren't the ones who got lucky — they're the ones who set the root explicitly, deployed PortFast and BPDU Guard on every access port, enabled Root Guard on distribution-facing uplinks, and verified their topology with
show spanning-tree detailbefore anything ever went wrong. That's the entire game: instrument it, own the root election, and protect your edge ports. The protocol handles the rest.