Reverse DNS lookup is the process of resolving an IP address back to a fully qualified domain name (FQDN). While forward DNS resolves names to addresses using A or AAAA records, reverse DNS goes in the opposite direction — from IP address to hostname. This mechanism is foundational to network troubleshooting, email deliverability, security auditing, intrusion detection, and logging pipelines across production infrastructure.
The technical backbone of reverse DNS is the PTR (pointer) record, stored in a special zone namespace called in-addr.arpa for IPv4 addresses and ip6.arpa for IPv6 addresses. Understanding how these zones are structured, delegated, and maintained is essential knowledge for any infrastructure engineer managing DNS at scale.
How Reverse DNS Works Technically
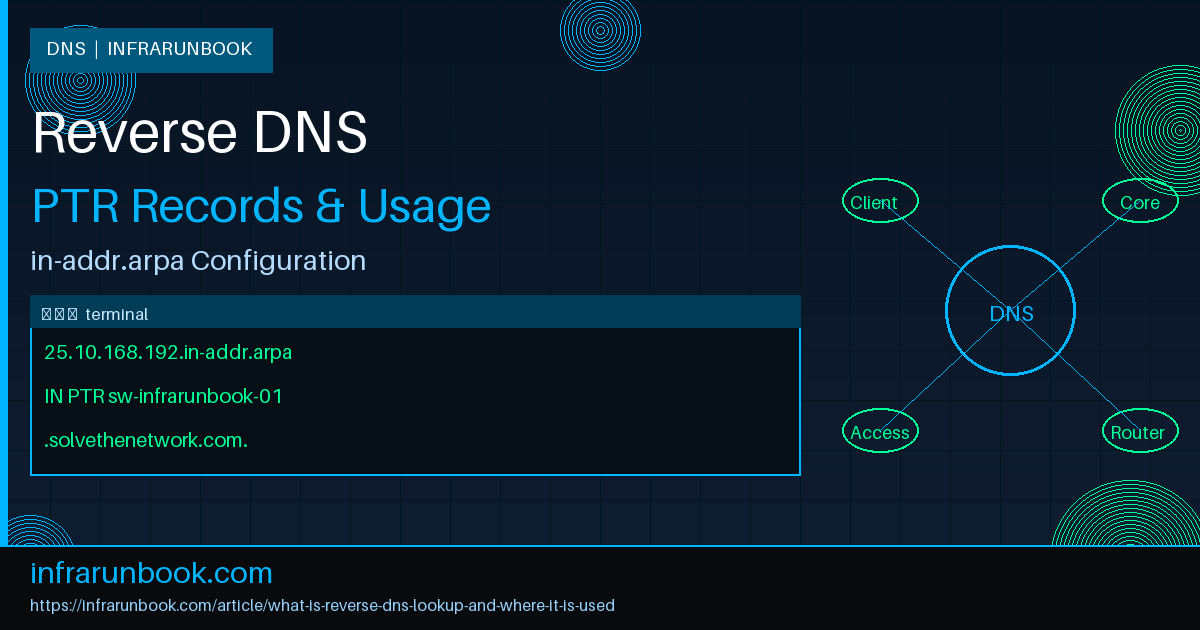
When a resolver performs a reverse lookup on the IPv4 address 192.168.10.25, it does not query that IP directly. Instead, it reverses the four octets and appends the in-addr.arpa suffix, constructing a query name:
25.10.168.192.in-addr.arpaThe resolver then queries for a PTR record at that name. If one exists, the DNS server returns the associated hostname. The reversal of octets is intentional — DNS zones are hierarchical from right to left, with the most-significant label on the right. Reversing the IP address maps address blocks to the same hierarchical structure used in forward zone delegation, allowing the same delegation model to apply to both directions.
For IPv6, the process is more granular. Each hexadecimal nibble of the address is reversed, separated by dots, and appended with ip6.arpa. For the address fd00::1 (fully expanded: fd00:0000:0000:0000:0000:0000:0000:0001), the reverse lookup name is:
1.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.d.f.ip6.arpaThis nibble-by-nibble expansion means IPv6 reverse zones can be very large, though in practice most organizations delegate at the /48 or /64 boundary.
Delegation and Zone Authority
Reverse DNS zones are delegated much like forward zones, but authority is coupled tightly to IP address allocation. For public IP space, Internet service providers and Regional Internet Registries (RIRs) such as ARIN, RIPE NCC, and APNIC are the authoritative holders of PTR delegation. When an organization receives a block of public IP addresses, the ISP can sub-delegate the corresponding reverse zone to the organization's own authoritative name servers, allowing that organization to manage its own PTR records.
For RFC 1918 private address space — 10.0.0.0/8, 172.16.0.0/12, and 192.168.0.0/16 — the internal DNS infrastructure handles reverse zones entirely. There is no external authority to consult. If your environment uses 192.168.10.0/24, you define and populate a zone named 10.168.192.in-addr.arpa on your internal BIND or equivalent resolver.
Configuring a Reverse Zone in BIND
The following shows how to declare a reverse zone for 192.168.10.0/24 inside BIND's named.conf:
zone "10.168.192.in-addr.arpa" IN {
type master;
file "/etc/named/zones/db.192.168.10";
allow-update { none; };
allow-transfer { 192.168.10.5; };
};The corresponding zone file at /etc/named/zones/db.192.168.10 contains the SOA, NS, and PTR records:
$TTL 86400
@ IN SOA sw-infrarunbook-01.solvethenetwork.com. infrarunbook-admin.solvethenetwork.com. (
2024031501 ; serial (YYYYMMDDNN)
3600 ; refresh
900 ; retry
604800 ; expire
300 ) ; minimum TTL
; Authoritative name server
@ IN NS sw-infrarunbook-01.solvethenetwork.com.
; PTR Records — last octet maps to FQDN
1 IN PTR gw-infrarunbook-01.solvethenetwork.com.
10 IN PTR dns-infrarunbook-01.solvethenetwork.com.
20 IN PTR mail-infrarunbook-01.solvethenetwork.com.
25 IN PTR sw-infrarunbook-01.solvethenetwork.com.Critical detail: Every FQDN in a PTR record must end with a trailing dot. Without it, BIND interprets the name as relative to the zone origin, producing a malformed pointer such as
sw-infrarunbook-01.solvethenetwork.com.10.168.192.in-addr.arpa— a common and difficult-to-spot configuration error.
Classless Reverse Delegation (RFC 2317)
When an ISP allocates a subnet smaller than a /24 — for example a /27 — they cannot delegate an entire class C reverse zone to the customer because they still own other addresses within it. RFC 2317 defines a classless delegation technique using CNAME records to route individual PTR lookups to a customer-controlled sub-zone.
For a customer receiving 192.168.10.64/27 (addresses .64 through .95), the ISP sets up CNAME records and an NS delegation in their zone:
; In ISP's zone for 10.168.192.in-addr.arpa
$ORIGIN 10.168.192.in-addr.arpa.
64 IN CNAME 64.64-95.10.168.192.in-addr.arpa.
65 IN CNAME 65.64-95.10.168.192.in-addr.arpa.
66 IN CNAME 66.64-95.10.168.192.in-addr.arpa.
; ... continues through 95
64-95 IN NS sw-infrarunbook-01.solvethenetwork.com.The customer then runs a zone named 64-95.10.168.192.in-addr.arpa on their own name server and populates it with PTR records for the addresses in their allocation. This approach is fully transparent to resolvers because they simply follow the CNAME chain.
Querying PTR Records
The standard tool for reverse lookups is dig with the
-xflag, which automatically constructs the in-addr.arpa query:
dig -x 192.168.10.25
; <<>> DiG 9.18.12 <<>> -x 192.168.10.25
;; QUESTION SECTION:
;25.10.168.192.in-addr.arpa. IN PTR
;; ANSWER SECTION:
25.10.168.192.in-addr.arpa. 86400 IN PTR sw-infrarunbook-01.solvethenetwork.com.
;; Query time: 1 msec
;; SERVER: 192.168.10.10#53(192.168.10.10)To target a specific authoritative server directly:
dig PTR 25.10.168.192.in-addr.arpa @192.168.10.10 +shortTo trace the full delegation chain for a public IP, use the
+traceflag:
dig -x 203.0.113.55 +traceUsing host for a quick check:
host 192.168.10.25
192.168.10.25.in-addr.arpa domain name pointer sw-infrarunbook-01.solvethenetwork.com.Where Reverse DNS Is Used in Production
Reverse DNS is not a purely diagnostic feature. It is actively evaluated and relied upon by a wide range of production systems. The following covers the most significant use cases.
Email Deliverability and FCrDNS
Most mail transfer agents (MTAs) perform a reverse lookup on the IP address of an incoming SMTP connection. If the connecting IP has no PTR record, or if the hostname returned does not forward-resolve back to the same IP, the message is likely to be rejected or aggressively spam-scored. This bidirectional check is called Forward-Confirmed reverse DNS (FCrDNS), sometimes referred to as a double-reverse DNS check.
The FCrDNS verification sequence is:
- Connecting IP: 192.168.10.20
- Reverse lookup → mail-infrarunbook-01.solvethenetwork.com
- Forward lookup of that hostname → must return 192.168.10.20
Both zones must be consistent. The BIND forward zone entry:
; In db.solvethenetwork.com
mail-infrarunbook-01 IN A 192.168.10.20And the reverse zone entry:
; In db.192.168.10
20 IN PTR mail-infrarunbook-01.solvethenetwork.com.Syslog and SIEM Log Enrichment
Log management platforms and SIEM systems — including Splunk, Graylog, and the Elastic Stack — routinely perform reverse DNS lookups to annotate event records with hostnames. A firewall log entry showing a connection from 192.168.10.25 becomes immediately actionable when enriched to show sw-infrarunbook-01.solvethenetwork.com. Without PTR records, analysts must cross-reference IP-to-hostname tables manually, significantly slowing incident response workflows.
Traceroute and Network Path Analysis
The traceroute utility performs a PTR lookup on every hop IP it discovers. Network operators routinely set descriptive PTR records on router loopbacks and transit interfaces to expose topology metadata — including site code, carrier, and geographic location — directly in traceroute output. This makes diagnosing routing loops, asymmetric paths, and blackholes significantly faster.
SSH Authentication Logging
When
UseDNS yesis set in sshd_config, the SSH daemon performs a reverse lookup on each connecting client IP and logs the resolved hostname alongside the username and key fingerprint. This adds a human-readable identifier to auth.log entries and can also feed into TCP Wrappers or host-based access control rules that match on hostnames.
Intrusion Detection Systems
IDS platforms such as Snort and Suricata, and next-generation firewalls, optionally resolve IP addresses when generating alerts. A PTR record that maps 192.168.10.25 to sw-infrarunbook-01.solvethenetwork.com immediately identifies the affected asset in the alert without requiring a secondary lookup in a CMDB or asset inventory.
Network Monitoring Dashboards
Monitoring tools such as Nagios, Zabbix, LibreNMS, and Prometheus node exporter rely on PTR records to populate display labels in dashboards. Without PTR records, every panel, alert, and graph shows raw IP addresses, making large-scale infrastructure significantly harder to interpret under pressure.
Anti-Spam and Reputation Scoring
Spam filtering systems including SpamAssassin, Rspamd, and commercial email security gateways incorporate PTR record checks as scoring factors. A sending IP whose PTR record matches the envelope domain and passes FCrDNS earns positive reputation points. A PTR record that resembles a consumer broadband assignment (e.g., containing patterns like
dynamic,
dhcp, or
pool) is a strong signal of a compromised host or improperly configured mail server and will be penalized accordingly.
Web Server Access Logs
Apache HTTP Server supports the
HostnameLookups Ondirective, and nginx can use the
$remote_addrcombined with a Lua resolver or the
ngx_http_core_modulelog format to resolve client IPs. While this is generally disabled in high-traffic environments due to added latency per request, it can be valuable in internal or low-traffic applications where the named client context is important.
Dynamic Reverse DNS with BIND and ISC DHCP
In environments where addresses are dynamically assigned via DHCP, PTR records must be created and removed automatically. ISC DHCP server integrates with BIND dynamic DNS updates using TSIG keys for authentication. A minimal dynamic DNS configuration:
# /etc/dhcp/dhcpd.conf
key "dhcp-tsig-key" {
algorithm hmac-sha256;
secret "dGhpcyBpcyBhIHNhbXBsZSBzZWNyZXQ=";
};
zone 10.168.192.in-addr.arpa. {
primary 192.168.10.10;
key dhcp-tsig-key;
}
zone solvethenetwork.com. {
primary 192.168.10.10;
key dhcp-tsig-key;
}
subnet 192.168.10.0 netmask 255.255.255.0 {
range 192.168.10.100 192.168.10.200;
ddns-updates on;
ddns-update-style interim;
update-static-leases on;
option domain-name "solvethenetwork.com";
option domain-name-servers 192.168.10.10;
}BIND must be configured to accept TSIG-authenticated dynamic updates for both the forward and reverse zones:
zone "10.168.192.in-addr.arpa" IN {
type master;
file "/etc/named/zones/db.192.168.10";
allow-update { key "dhcp-tsig-key"; };
};
zone "solvethenetwork.com" IN {
type master;
file "/etc/named/zones/db.solvethenetwork.com";
allow-update { key "dhcp-tsig-key"; };
};Reverse DNS Troubleshooting Checklist
When PTR records are not resolving correctly, work through the following diagnostic sequence:
# 1. Validate zone file syntax before loading
named-checkzone 10.168.192.in-addr.arpa /etc/named/zones/db.192.168.10
# 2. Validate named.conf syntax
named-checkconf /etc/named.conf
# 3. Query authoritative server directly (bypass caches)
dig -x 192.168.10.25 @192.168.10.10 +short
# 4. Check SOA serial to confirm zone is current
dig SOA 10.168.192.in-addr.arpa @192.168.10.10
# 5. Trace the delegation chain (public IPs)
dig -x 203.0.113.55 +trace
# 6. Confirm FCrDNS forward/reverse consistency
host 192.168.10.20 && host mail-infrarunbook-01.solvethenetwork.com
# 7. Inspect BIND logs for zone load errors
journalctl -u named --since "30 min ago" | grep -i "error\|failed\|refused"Common Configuration Pitfalls
- Missing trailing dot on PTR targets: A PTR record pointing to
sw-infrarunbook-01.solvethenetwork.com
without a trailing dot is interpreted as relative to the zone origin, producingsw-infrarunbook-01.solvethenetwork.com.10.168.192.in-addr.arpa
. Always terminate FQDNs in zone files with a dot. - Serial not incremented after changes: Secondary name servers use the SOA serial to detect zone changes. If you edit a zone file but forget to increment the serial, secondaries will not pull the updated data. Use the YYYYMMDDNN format and increment NN for multiple changes on the same day.
- ISP delegation not configured: For public IP ranges, you cannot resolve PTR records until the ISP either enters them directly or delegates the reverse zone to your name servers. This is the single most common cause of reverse DNS failures in cloud and colocation environments.
- Zone name typo: Declaring the zone as
10.168.192.in-addr.arpa
when the actual prefix is 192.168.10.0/24 is correct, but operators frequently transpose octets when moving between subnets. Double-check the octet reversal for each new subnet. - Overly long TTLs on dynamic environments: If DHCP leases rotate frequently, long PTR TTLs leave stale entries in resolver caches. Use a TTL of 300–600 seconds for dynamically assigned ranges and longer TTLs (3600–86400) only for static infrastructure.